In our last post, we discussed “Game Theory In Blockchain Technology: Key To Strategic Decision Making.” Few of the takeaways from the earlier post are:
Game theory in blockchain technology has a dual role to play i.e. inward & outward. Inward is to apply the principles of the theory to the blockchain protocol. Outward is to integrate the strategic decision-making model with the business’ process.
We discussed various types of models & games like Stackelberg & Stochastic respectively to name a few. We discussed “The Prisoner’s Dilemma” and various types of equilibrium like Markov perfect equilibrium & Nash equilibrium.
Taking the Game Theory thread forward, we shall be discussing it’s application in the blockchain security by focusing on specific scenarios.
Blockchain Security: Application of Game Theory
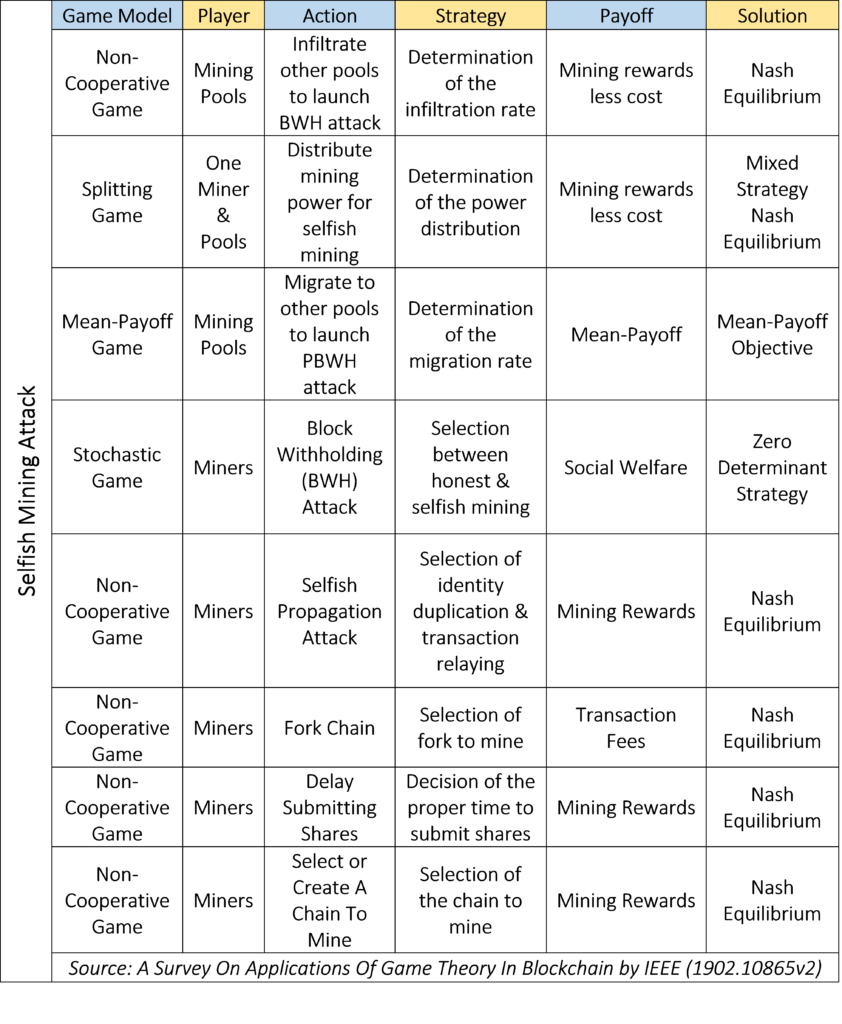
Selfish Mining Attack
A power undermining strategy in Proof of Work (PoW) based blockchains where the attackers may either withhold the newly mined blocks or hold & then release the block at a proper time. Doing so the attacker increases its probability of finding the new block while other miners invest their computational power to discover an already discovered block.
Markov Decision Process (MDP) can be applied to analyze the strategies and utility of the individual players and the pools. What MDP does not take into account is interaction among the multiple players. This is where game theory could be applied.
A players utility is the function of the computational power and the infiltration rate. The objective of a player is to optimize its infiltration rate. The utility function is proved to be concave through the application of the second-order derivative. That means there exists a Nash equilibrium where neither player can improve its utility by changing its strategy i.e. infiltration rate. The scenario is similar to the famous Prisoner’s Dilemma and could be termed as the Miner’s dilemma wherein a miner will always choose one of the two scenarios.
The first solution is miners joining a private pool that will not launch any attack.
The second solution is miners performing a zero-determinant (ZD) strategy. ZD strategy is about maximizing the pools profit than an individual’s own profit.
Undercutting Attack
Undercutting attack is when a miner fork the head of the chain actively and leaves transactions unclaimed selectively to maximize the profit. Because rewards are only attached to block creation, it is profitable for any miner to extend the blocks that have the most available transactions fee rather than following the entire chain. An undercutter may gain nothing if the blocks are not in the longest chain. Since every miner adopts an undercutting strategy to maximize its profit, there exists a Nash equilibrium for all the miners.
Majority Attack
Distributed consensus is the defining element of a blockchain’s security. This means no single miner can hold more than 50 percent of the network’s computational power. Majority attack is also known as a 51 percent attack wherein a miner invests in the computational power and succeeds in possessing more than 50 percent of the power. In case of such attacks, mining on the forked chain may happen. To maximize the reward, each miner aims to extend selectively any of the existing branches or to create a new branch, given the strategy of the other miners. A non-cooperative game could thus be applied wherein mined block would not achieve the Nakamoto consensus and thereby be orphaned. Hence, following the longest-chain would be the best strategy for all the miners. Therefore, the game has a Nash Equilibrium in which all the miners extend the longest chain.
Denial of Service (DoS) Attack
The distributed structure of the peer-to-peer network in blockchain means that every miner can observe the Proof of Work (PoW) done by their peer. In the case of a P2P network attack, the attacked miners resources may be exhausted. The attacked miner may not complete the mining process in that case. Such an attack is known as the Denial of Service (DoS) attack. To maximize the mining reward the mining pool can choose to either trigger the distributed DoS attack or invest in additional computational power. To analyze the interaction among the pools, a non-cooperative game could be adopted. The Nash Equilibrium is reached when the mining pools have no incentive to launch the DDoS attack, applying the principle of the second-order derivative.
Where is blockchain headed
The blockchain technology is finding applications in many new areas like edge networks, cloud computing, information sharing, and e-business. The blockchain-based protocol has given birth to new schemes in Healthcare, Banking & Finance, Insurance, manufacturing, agriculture, and various other industries.
In our next post read about “Application of Game Theory Over The Blockchain Layer“.
Follow Us on LinkedIn
Follow Our Showcase Pages At FutureTech Lab, Everything Blockchain, and Digital Workplace Transformation

3 Comments